Count number of tables in the database – MySQL

Determining the number of tables that are contained in a MySQL database is very straight-forward, although it is an often asked question. The simplest way to accomplish this is using…
Read more
Determining the number of tables that are contained in a MySQL database is very straight-forward, although it is an often asked question. The simplest way to accomplish this is using…
Read more
Want a quick and dirty way to Truncate all the tables in a MySQL DB? You can use the following one line script. mysqldump -ppassword YourDBName –no-data dumpfile | mysql…
Read more
There are multiple ways in which to remove all data from a MySQL Table. The first is to use the DROP TABLE command, which will remove the entire table with…
Read more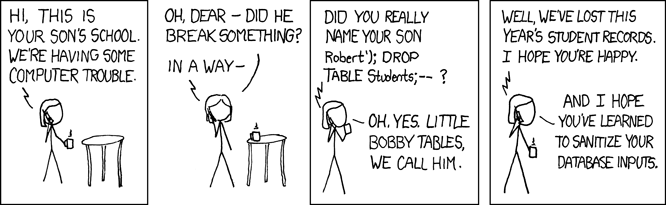
SQL injection vulnerabilities are often been described as the most serious threat for Web applications, regardless of what language they are written in . Web applications that are vulnerable to…
Read more